City of Boston and Washington State Experiences with Design and Implementation with Single Sign On
This blog summarizes an event exploring how the City of Boston and Washington State are designing and implementing Single Sign-On (SSO) systems to simplify access to government services.

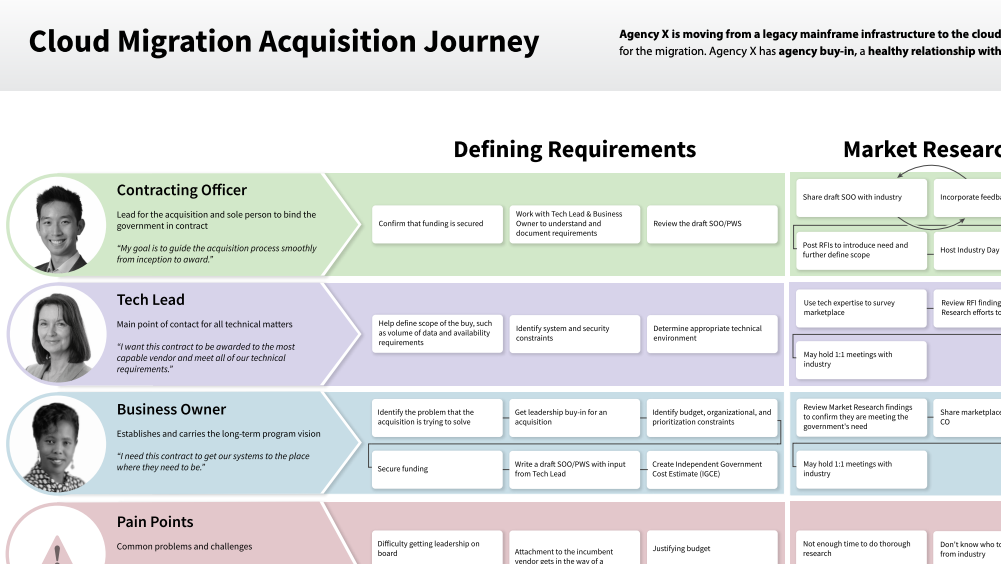
In this event, speakers Wendy Wickstrom (Chief Digital Experience Officer, Washington Technology Solutions), Hannah Burn (Customer Experience Lead, Washington Technology Solutions), Gretchen Grozier (Director of Identity & Access Management, City of Boston), and Greg McCarthy (Chief Information Security Officer, City of Boston) discussed how governments are looking to revamp or develop Single Sign-On (SSO) portals to make accessing government services easier. SSO is an authentication framework that enables multiple applications or services to use the same authentication session. Organizations such as universities and governments use it to let students, employees, or residents access associated services with one set of credentials. From Departments of State to permitting agencies, state and local jurisdictions are increasingly developing SSOs for their residents. For example, in late 2024, our team found that 19 states had integrated SSOs into their benefits portals for state benefits applications in core programs.
While SSOs primarily enable residents to create and use a single login or account across multiple distinct government agencies, they can also incorporate identity proofing—creating a verified digital identity for a resident to use across multiple services. Because of its many applications, getting the set-up right for a specific context and set of residents matters. If high standards of identity proofing and authentication are required with SSO account creation, it can block clients from doing low-risk activities and cause barriers to access. Additionally, developing an approach that works for multiple agencies requires both technical coordination and high stakeholder engagement.
Main Points
- The City of Boston, Massachusetts and Washington State are both pursuing SSO portals to simplify access to government services, though they are approaching the work from different starting points.
- Boston is building its first SSO portal, driven by Mayor Michelle Wu’s vision to move services out of City Hall.
- Washington State is modernizing SecureAccess Washington (SAW), a 20-year-old authentication system, with a revamped focus on user experience and usability.
Lessons Learned
- Large SSO goals must be broken down into manageable, achievable phases.
- Trust cannot be assumed; governments must actively communicate the purpose, value, and data practices of SSO systems to residents.
Actionable Takeaways
- Start with a clearly-defined pilot scope based on technical feasibility, agency readiness, and existing vendor timelines.
- Break SSO work into concrete roles and responsibilities, so tasks are embedded into people’s actual jobs.
- Evaluate whether existing identity verification tools can be reused before building new ones.
- Integrate user experience research early and continuously, especially during system transitions or redesigns.
In Boston, Grozier and McCarthy are working on creating the city’s first SSO portal to streamline processes and simplify how people work with the city, which started as part of Mayor Michelle Wu’s push to get city services out of City Hall. Grozier and McCarthy note that much of the development was made possible through strong executive support, including from Mayor Wu. Meanwhile, in Washington State, SAW—fondly nicknamed “the big green monster—was launched 20 years ago and is now being revamped with a focus on improving user experience. These two vastly different experiences enable us to learn how to develop SSO portals and identify key areas to focus on in the development process.
In Boston and Washington State, key challenges included gaining community trust, identity verification, and finding a starting point for this large task. Both governments highlighted the importance of dreaming big but starting small, as SSO projects can overwhelm system-building tasks and data backlogs. To manage this, teams focused on core needs before expanding to more complex functions. This helped break large goals into concrete, assignable jobs rather than abstract mandates. Identity verification emerged as a major pain point, with debates about building new systems or leveraging existing ones, verifying only high-risk data, and minimizing user friction. Underlying all of this was a trust challenge as governments recognized the need to clearly communicate the purpose of platforms through effective marketing and transparent communication about how constituents’ personal data and technology would be used.
Overall, this session highlighted that SSOs are not just a technical upgrade, but a transformation in how governments think about service delivery, trust, and user experience. Indeed, Boston and Washington State’s experiences offer valuable lessons for any state or local government just getting started.